The Problem
- Attackers can hide command-and-control signals in ordinary DNS queries, bypassing standard network defenses.
- Organizations face huge volumes of DNS data, and manual monitoring can’t catch subtle malicious patterns.
- Stealthy DNS “tunnels” blend into normal traffic, often escaping detection until significant damage is done.
The Solution
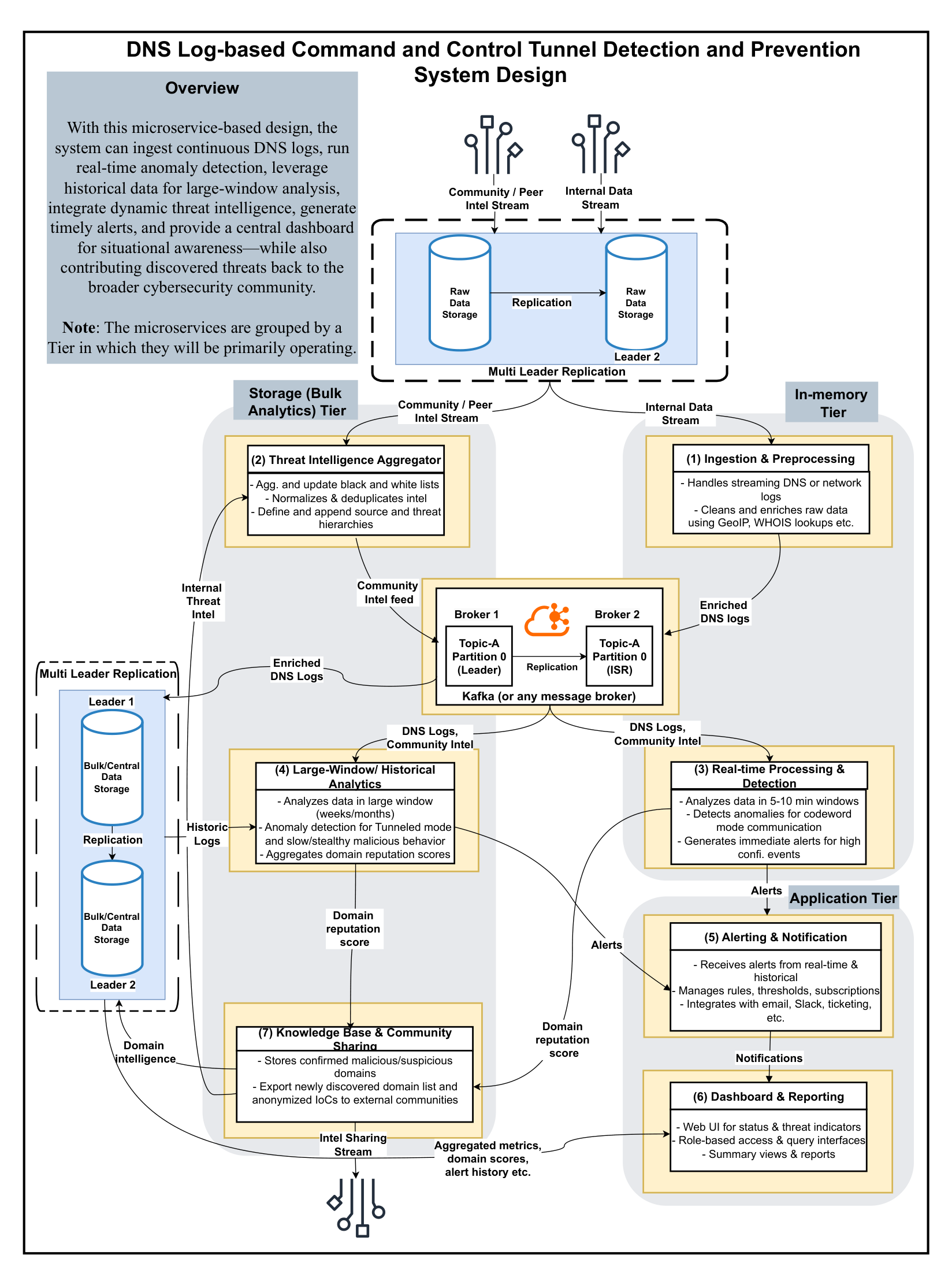
- Built a microservice pipeline to continuously ingest and enrich DNS logs (e.g., adding GeoIP and WHOIS context) for live analysis.
- Implemented multi-scale anomaly detection: short-window analytics to flag immediate threats and long-window analytics to uncover slow, stealthy DNS tunnels.
- Integrated threat intelligence feeds to flag known malicious domains and deployed a real-time alerting dashboard for security teams.
Architecture Overview
- Modular Microservices: Independent services handled data ingestion, threat intel updates, anomaly detection, analytics, alerting, and the user interface.
- Streaming Pipeline: A Kafka message broker streamed DNS events between services, enabling scalable, real-time processing of log data.
- Tiered Storage: Combined in-memory caching for instant analysis with a persistent datastore for historical pattern detection over longer windows.
- Tiered Deployment: Services were grouped by function (data ingestion, analysis, storage, presentation) to optimize performance and scalability.
- Resilient Design: The microservice architecture allowed isolated scaling and updates, ensuring robust, fault-tolerant operation of the system.
Results and Impacts
- Achieved near-instant alerts for emerging DNS-based threats, vastly reducing attacker “dwell time” in networks.
- Improved detection accuracy by combining real-time anomaly flags with historical context and threat intelligence (catching both abrupt spikes and subtle slow attacks).
- Delivered actionable dashboards and alerts that empower security teams to swiftly contain incidents and share new threat indicators with the broader community.
Skills and Tools Used
| Technique/Skill | Tools/Implementation |
|---|---|
| Streaming & Processing | Apache Kafka for high-volume, real-time DNS log ingestion |
| Microservices & DevOps | Containerized services (Docker) for scalable, modular deployment |
| Data Enrichment | GeoIP and WHOIS lookups to add context to DNS query data |
| Threat Intelligence | Integrated domain blacklists/whitelists via APIs and databases |
| Visualization & Alerting | Interactive security dashboard and automated notification system |
Cross-Project Capabilities
- Real-Time Analytics: Streaming anomaly detection methods here can be reused for live data monitoring in other domains (e.g., social media trends).
- Data Fusion: Combined internal logs with external intel feeds, mirroring multi-source integration techniques used in other projects.
- Dashboard Design: Created intuitive security dashboards – a skill transferable to other analytics platforms (such as public health dashboards).
Published Papers/Tools
- Internal Design Blueprint (2025): Architecture and findings documented in an internal presentation for the cybersecurity team.
- Proprietary Solution: This project was delivered as an internal security tool (no public release due to sensitivity).